Afraid of the Possibility of Imminent Cyber-attack? Security Testing is Key!
Cybersecurity Ventures expects global cybercrime costs to grow by 15 percent per year over the next five years, reaching $10.5 trillion USD annually by 2025
Cybersecurity is quickly becoming more of a business expense than a technical issue. To tackle the imminent threat, it’s imperative for businesses to ensure that the right resources are on the job and that the right tools are in place. Often, a security breach cannot be altogether avoided; however, it is imperative that the issue is dealt with by taking immediate action. In the event of a delay, the reputation of the organization is severely impacted, that too, for a long time to come.
Many large corporations in the United Kingdom are not taking enough precautions in order to avoid or immediately deal with an imminent cyberattack. Statistics show that over the past year, over half the UK businesses have been victimized by a cyber-attack. The good news is that many of these businesses admitted to being certain about returning to business quickly after such an attack.
Recent reports suggest that banks in Britain are avoiding reporting the true magnitude of imminent cyber-attack cases. Although they deal with the imminent threat on a legal level, for the most part, to avoid penalty and embarrassment, the banks often do not reveal the whole picture. Instead, they opt for damage control and continue functioning without batting an eyelid. The banks go as far as to conceal severe cyber security breaches for fear of public reaction.
CYBER-ATTACKS
Imminent cyber-attack on a product or service often refer to data compromise and make consumers vulnerable to fraud by exposing their details. Because the most benefit that can be derived from a fraud is monetary in nature, several E-commerce organizations and banking institutions remain prime targets.
Distributed Denial of Service (DDoS) attacks continue to target E-commerce organizations. In particular, the attacks attempt to stall website operations through server crashes and application layer attacks. While server-down issues can be quickly resolved, application-layer attacks are harder to detect. This is because they focus on one internal part of a website, eventually leading to an application crash.
According to an internet retailer report, about 40.0% of the entire SQL injection attacks throughout that period specifically targeted retail websites. In an SQL injection, hackers supplement bits of malicious code into a particular data entry field. For example, one that requests a customer’s address. If a database is not appropriately configured, there is imminent threat of malicious code transmit into the database’s contents to the attacker. In general, offenders on cyberspace have turned out to be more active as the years pass by.
As digital technology takes over most businesses, consumer data remains key to formulating and executing many business strategies. Apart from banking institutes and E-Commerce organizations, many other businesses are also increasingly aware of the need to have a robust imminent cybersecuritysecurity threats testing system in place.
Along with the frequency, the sophistication of the cyber-attacks is also on the rise; and the expertise and expense involved in curtailing the attacks is burning holes in company pockets. Reports suggest that the number of records exposed in data breaches rose to a whopping 97% in the last year. Medical data and business information dealing with intellectual property were theorized to be the prime targets.
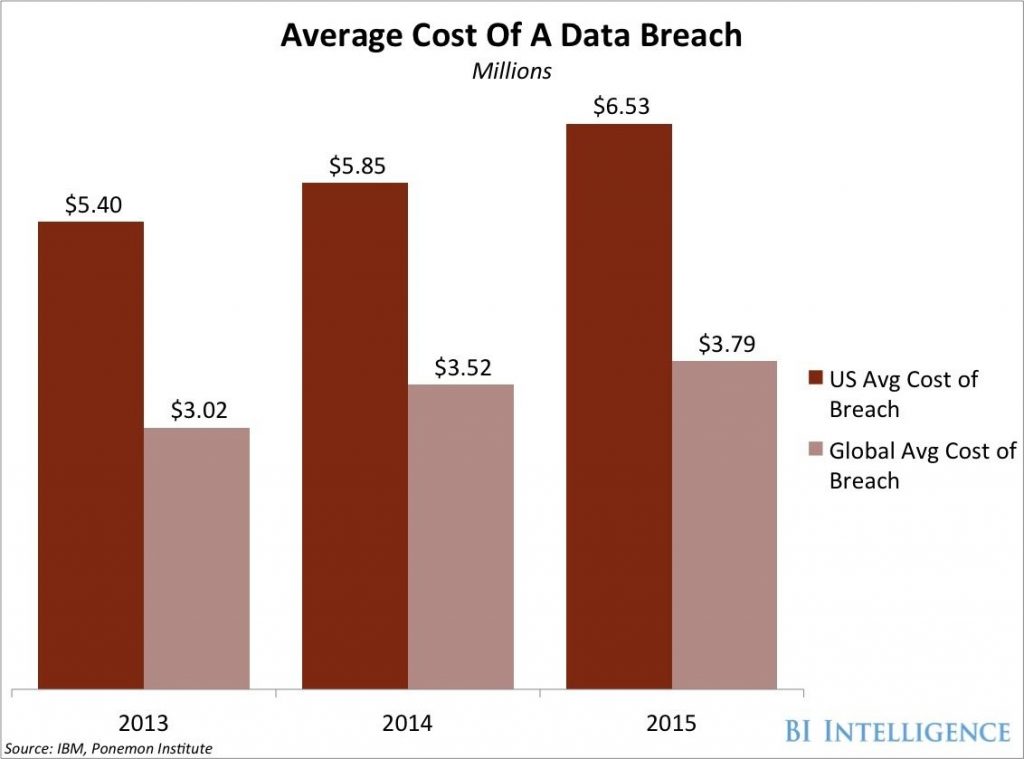
Even though necessary precautions are taken, businesses can never hope for absolute cyber security. The following graph gives an insight regarding the average cost of a data breach, for the United States, as well as at a global level. The trend shows that the cost is steadily increasing, as 2015 tops the chart with a monstrous $6.53 Million.
[Tweet “According to @IBM’s study on cost of #databreach, The average cost of a #databreach grew from $4.35M IN 2022 to $4.45M in 2023. #Cybersecurity”]
Cyber insurance plans are expected to double over the next four years, as demand for them steadily rises. Cyber insurance plans cover a range of costs and revenue lost from downtime and notify customers affected by a data breach, providing identity theft protection for the affected customers.
The following list highlights some of the biggest cyber-attacks over the past three years:
- 2021 – Colonial Pipeline, one of the largest and most vital oil pipelines in the U.S, fell prey to a ransomware attack that compromised its digital systems, leading to a multi-day shutdown. During a brief two-hour period, the attackers exfiltrated 100 gigabytes of data. Subsequently, the assailants deployed ransomware across the Colonial Pipeline’s IT network, impacting various systems, including billing and accounting functions.
- 2022– Marriot, the international hotel group, encountered a data breach where an unidentified threat actor infiltrated a computer server at a Maryland-based Marriott hotel. The breach resulted in the unauthorized access and exfiltration of 20 gigabytes of sensitive data, including guests’ credit card details and confidential information about guests and employees.
- 2023 – Regal Medical Group, headquartered in southern California, reported falling victim to a ransomware attack. The incident, described as a “ransomware cyberattack,” could compromise the data of over 3.3 million individuals, as indicated by the health department. The breach also affected Regal’s affiliated entities.
WHY SECURITY TESTING?
Security testing, a significant part of software testing, anticipates susceptibilities in the system and strives to protect its data and resources from possible intruders.
The consequences of a potential security breach are momentous: legal liability, loss of revenues, loss of customer trust, and damage to credibility. Security testing guarantees the reputation of organizations, the confidence of customers, privacy of sensitive data, and, inevitably, trust.
“Securitytesting assures the reputation of organizations, the confidence of customers, privacy of sensitive data, and, inevitably, trust.”
There are four focus areas to be considered in the process of security testing:
- Network security
- System software security
- Client-side application security
- Server-side application security
Cybercriminals are very innovative and keep developing newer and advanced ways of breaking into systems and applications. The mere process of security testing is seldom the only measure to test how secure an application really is. However, it is strongly suggested that cyber security testing is encompassed in the standard application life cycle. In a world teeming with hackers, trust plays a huge role for consumers.
The Challenges
There are quite a few challenges associated with Cyber Security Assurance Services:
- Capacious lines of code need to be duly tested in order to find susceptibilities in short test cycles
- There is a prerequisite for end-to-end knowledge of the entire application ecosystem, which comprises of numerous platforms across the presentation, data tiers, logic, and the associated threats and vulnerabilities
- There are too many false negatives and false positives that are caused by using a tool-based scan method
- There is an inherent need for testing professionals who are accredited and certified and possess ethical hacking skills
- There is a definite lack of guidelines and security standards that are required in order to address emerging technology
“The need for #testing professionals that are accredited and possess #ethicalhacking skills proves to be a challenge for #Securitytesting.”
In Conclusion
What most organizations lack today in is a team that can completely focus on performing cyber security and the other critical forms of tests such as digital, cloud, automation, software, performance, big data, and more. Due to this, many applications are launched in the market without being tested thoroughly. This has led to the critical need for pureplay independent software testing vendors who can provide the focused approach to testing so desired.
The Cyber Security Testing services provided by Cigniti Technologies comprise an in-depth security analysis maintained by reports and dashboards that are comprehensive, in addition to remedial measures for any issues that may be found. Cigniti also has exceptional expertise in Security Testing for mobile applications, web applications, web services, and software products, both over the cloud, as well as on premise.
Over the past decade, Cigniti has assembled a knowledge repository, capabilities, and test accelerators, thereby leveraging the experience of working on over a hundred engagements, using latest industry standards (OWASP, etc.) and proprietary testing methodologies. Our team leverages passive security testing techniques (Social Engineering, Data Privacy, Architectural Risk Analysis, etc.) and active security testing methods (Ethical Hacking, Threat Modelling, etc.) using a combination of proprietary security, commercial, and open source testing tools.
To know more about the array of cyber security services and solutions we provide, visit our website and contact our experts.





Leave a Reply