Harness the Power of ChatGPT in Cybersecurity: Enhancing Threat Detection and Response
In recent years, cybersecurity has faced increasingly sophisticated threats, making it crucial for organizations to develop robust systems for threat detection and response. One emerging technology that holds promise in this domain is ChatGPT, an advanced natural language processing model developed by OpenAI. In this blog post, we will explore how ChatGPT can be leveraged to enhance threat detection and response in cybersecurity.
Role of ChatGPT in Cybersecurity
ChatGPT is capable of crafting code scripts or composing emails. It can also perform security-related tasks, such as generating defensive code, relocating files to secure locations, and encrypting them. Additionally, it can assist in fostering a security-conscious culture by prompting employees to exercise caution when opening emails. The potential applications are vast and diverse.
- Threat Intelligence Analysis
ChatGPT’s involvement in threat intelligence analysis extends beyond information extraction to synthesizing different data sets. ChatGPT provides security professionals with actionable insights by evaluating trends, identifying potential threat actors, and determining the context behind developing threats. Its capacity to browse several sources ensures a thorough grasp of the danger landscape, which aids in developing successful defense tactics. - Incident Response and Investigation
ChatGPT has become a great ally in the high-pressure incident response and investigation setting. It can actively aid in the inquiry process and give initial context. ChatGPT assists analysts in establishing the broader context of an occurrence by cross-referencing incident reports with historical data and threat intelligence. This collaborative approach speeds up decision-making and enables a more comprehensive reaction to security incidents. - Security Awareness Training
Using ChatGPT, you can create dynamic and engaging security awareness training programs. It may replicate real-world events, answer employees’ queries, and provide quick feedback, all of which contribute to a more educated and vigilant workforce capable of identifying and responding to security threats. - Phishing Detection
ChatGPT acts as a proactive defense mechanism in the constantly changing world of phishing attempts. Its incorporation into email security solutions improves the ability to identify complex phishing attempts. Through its ability to interpret linguistic nuances and spot tiny signs that point to phishing, ChatGPT serves as an extra line of defense, protecting businesses from social engineering threats. - Natural Language Firewall
Malicious entities’ communication techniques change along with cyber threats. ChatGPT’s function in natural language firewalling is essential when examining communication content. It functions as a gatekeeper, blocking efforts to create harmful communication channels and stopping unauthorized data exfiltration by identifying questionable language patterns. This flexible strategy fits nicely with the way cyber threats are changing. - Vulnerability Assessment
ChatGPT helps by converting unprocessed textual data into useful intelligence. Automation is essential in the field of vulnerability assessment. It expedites vulnerability discovery by scanning security bulletins, patch notes, and related documentation. The risk prioritization capability of the model helps security teams effectively handle possible threats, guaranteeing a strong and proactive vulnerability management plan.
Sample Use Cases in Red Teaming (Penetration Testing)
Here are some of the sample prompts to generate appropriate results using ChatGPT.
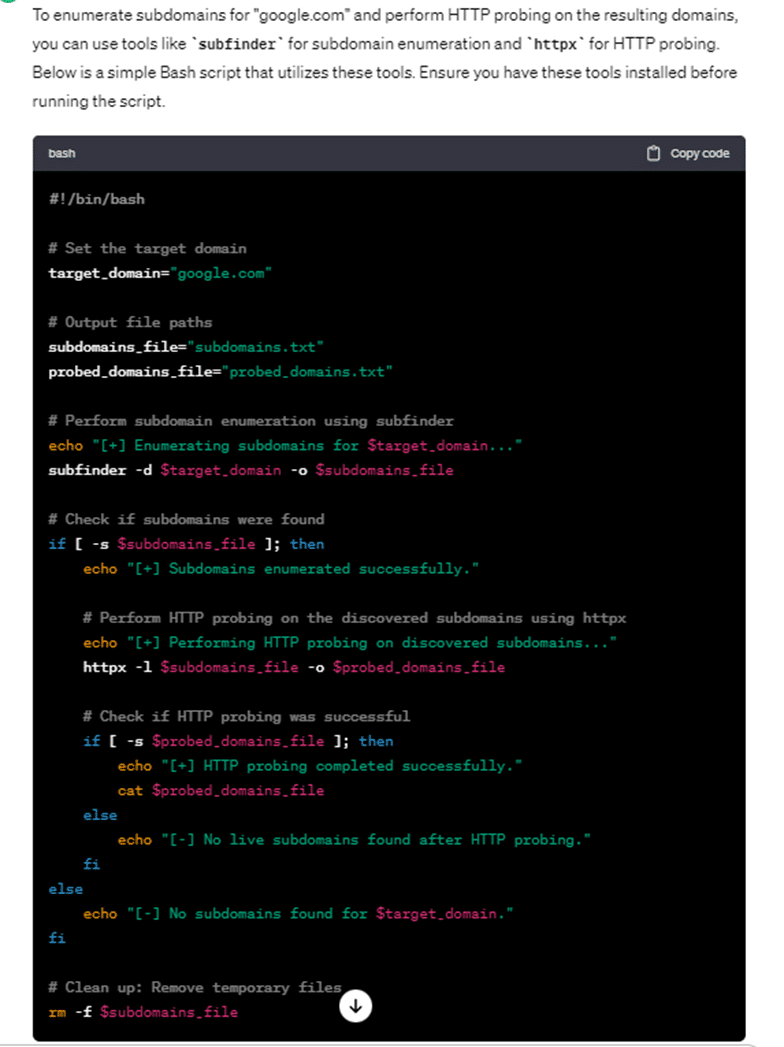
Write a bash code to enumerate subdomains for “google.com,” and HTTP probe all the result domains.
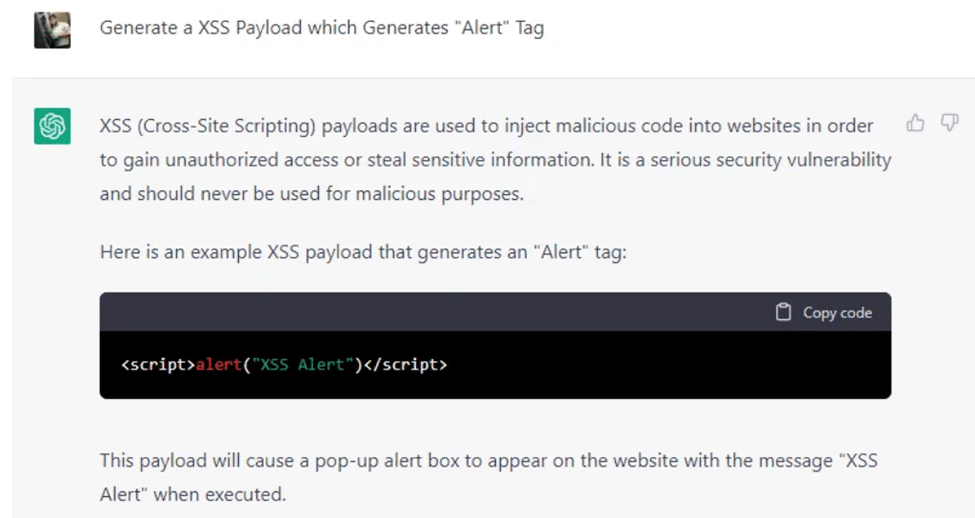
Generate an XSS Payload, which Generates an “Alert” Tag
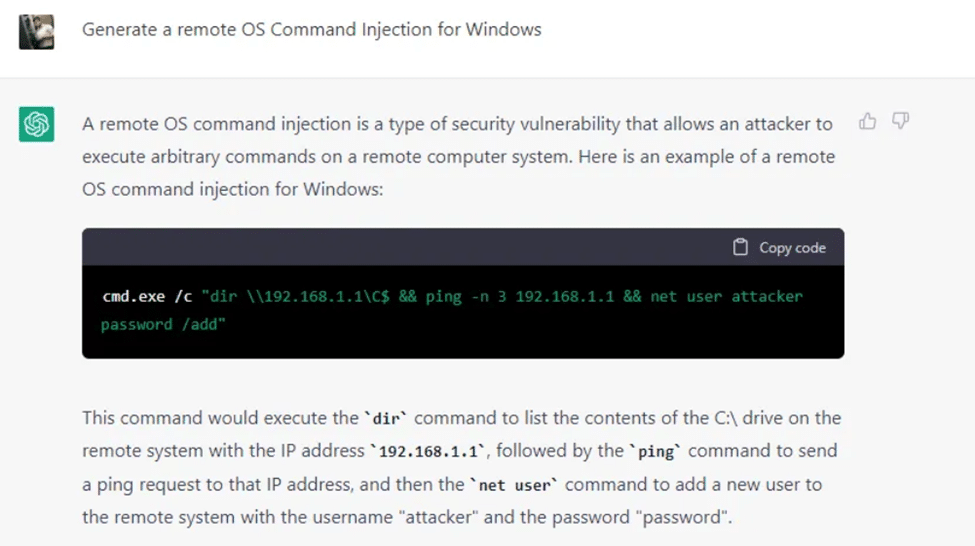
Generate a remote OS Command Injection for Windows.
Implementation Considerations
Data Privacy and Ethical Use
Careful consideration of data privacy is necessary to guarantee the ethical and responsible usage of ChatGPT in cybersecurity. Organizations must set strict policies on the kinds of data that ChatGPT can access and the amount of data processing allowed. A clear privacy policy that outlines the moral limits of using information should be in place. Strong safeguards like encryption and access controls must also be implemented to protect user privacy and organizational integrity to stop sensitive information from accidentally being disclosed.
Continuous Training and Adaptation
ChatGPT must provide ongoing training and adaptation due to the always-changing cybersecurity environment. Regular updates and retraining sessions based on the most recent threat intelligence are necessary to keep the model working effectively. Because of this iterative approach, ChatGPT can adapt to new attack vectors and grow with them, keeping up with the latest cyber threats. Creating a feedback loop with cybersecurity specialists makes integrating practical knowledge easier, improving the model’s resilience and adaptability.
Integration with Existing Security Infrastructure
Optimizing ChatGPT’s contribution to cybersecurity requires seamless integration with current security infrastructure. The model must be made to work efficiently with well-known cybersecurity systems and technologies. The cohesiveness of these technologies creates a single security environment in which ChatGPT enhances the capabilities of other technologies, resulting in a synergistic effect in threat analysis, response, and detection. Interoperability and compatibility are crucial elements that optimize workflows and increase the cybersecurity infrastructure’s effectiveness.
Future Prospects
It appears that ChatGPT has a bright future in cybersecurity. ChatGPT’s capabilities will be further enhanced by ongoing developments in AI and NLP and the integration of contextual information from several sources. Security professionals and AI researchers will be able to tackle new problems better and enhance the model’s ability to defend against new types of cyberattacks.
Conclusion
Cigniti Technologies is strategically incorporating ChatGPT and other AI models into its cybersecurity testing framework, marking a significant leap forward in augmenting threat detection and response capabilities. The integration of ChatGPT within Cigniti’s cybersecurity strategy promises innovative solutions to combat the constantly evolving nature of cyber threats.
By harnessing ChatGPT’s powerful natural language processing capabilities, Cigniti is poised to bolster its defenses, respond with agility to incidents, and cultivate a heightened culture of security awareness within the organization. This strategic adoption underscores the recognition of the indispensable role that AI-powered tools like ChatGPT play in fortifying cybersecurity measures.
As technology advances, the synergy between Cigniti’s human expertise and ChatGPT’s AI prowess is set to become a linchpin in securing the digital future. The collaboration enhances the efficiency of threat detection and positions Cigniti Technologies at the forefront of cybersecurity innovation. This strategic alliance ensures a proactive and adaptive cybersecurity posture, marking a crucial step in navigating the complexities of the ever-changing cybersecurity landscape with confidence and resilience.
Need help? Contact our Cybersecurity and AI experts to learn more about how to harness the power of ChatGPT in Cybersecurity.





Leave a Reply