Ransomware made you WannaCry? 10 Things the Disaster taught
200,000+ victims, 150 countries affected, Microsoft Windows XP Operating System attacked, ATMs shut, and online transactions stalled.
The experts have warned that the threat is not yet over.
On May 12, 2017, the world was stormed by a Ransomware aptly named WannaCry that was programmed to encrypt all data on a system for unlocking which, the hackers demanded a hefty ransom.
The question remains, can such data breaches be mired or totally clogged with anti-virus programs, or there is a serious need for a coherent Security Testing strategy?
Though Cybersecurity firms have warned organizations and individuals against paying the bitcoin ransom, the hackers behind the malware have already made a minimal gain of $60,512.82. However, Cyber security experts and connoisseurs from the industry maintain that such attacks on the internet will continue to grow and threaten the core existence of the web in the global socio-economic sphere.
Interestingly, according to Reuters, the motive of the WannaCry Ransomware attack was not necessarily to make money, but to create a random disruption across the Web world. Russia, Taiwan, Ukraine, and India are said to be the worst affected countries, specifically in the scenario where companies or individuals have been relying on unsupported or pirated versions of Microsoft Windows.
Experts across the web world are coming up with quick remedies to safeguard against the virus. For instance, installing reputable antivirus software, regular back-up, enabling pop-up blocker, being alert over emails, alerting authorities in case of an attack, and the extreme amongst all – to remain disconnected from the internet. However, detaching from the Internet is almost like breaking away from your basic business requirement.
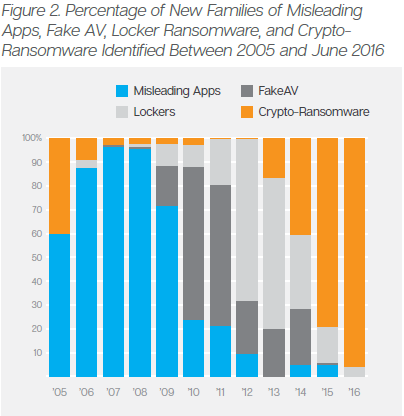
Source: An ISTR special report: Ransomware and Businesses 2016
Special report by Symantec on Ransomware and Business has noted that, ‘The proportion of new variants classified as crypto-ransomware was growing year-on-year. That trend has continued into 2016 and, so far this year, all bar one of the new ransomware families documented by Symantec are crypto-ransomware.’
Knowing so well that such attacks will not stop and only intensify, enterprises today are in a serious need to build applications/software that are tested rigorously for their security and are, at the same time, able to alert the users against any probable cyber-attack.
How can a comprehensive Security Testing plan work, and what have we learnt from this recent attack to build a robust plan? We discuss 10 things this disaster has taught us about avoiding malware attacks on the system.
1) Follow a Four-phase Approach to Cyber Security
F-Secure, a cyber-security and privacy company based in Helsinki, Finland, suggests that one of the best approaches to cyber security is the following four-part one: Predict, Prevent, Detect, and Respond
This essentially translates to: predicting by performing an exposure analysis; preventing by deploying a defensive solution to reduce the attack surface; detecting by monitoring infrastructure for signs of intrusion or suspicious behaviour, and responding by determining how a breach happened and what impact it had on systems.
2) Remain Cautious While Opening Attachments
The most common ways of installing the virus are through compromised emails and websites. It might be elementary for many now to be extremely cautious while opening an attachment from unknown email addresses. However, it is surprising to note that sheer curiosity has driven many unsuspecting recipients to open attachments, causing malware attacks. Along similar lines, it is crucial to stop clicking links that you don’t trust, and stop downloading software from unknown sources.
Watch out especially for “social engineering”, which is an email that looks like it’s coming from your bank, a tech support scam, or a fishy social media campaign, cybercriminals have gotten rather deft at tricking even tech-savvy surfers.
Awareness while handling email plays a major role in thwarting possible malware, as malicious attachments are often disguised as benign promotional offers.
3) Do not call/take calls from fake tech support numbers
Tech support scams have time and again proved to be the bane of our existence. These often involve pop-ups from fake companies offering to help you with a malware infection. How to identify that they are fake? A real security company would never market to you via pop-up saying they believe your computer is infected.
They would particularly not serve up a (random) 1-800 number and charge money to fix it. If you have security software that detects malware, it will confirm such a finding in your scan, and it will not encourage you to call and shell out money to remove the infection. Those are the characteristics of a scam trying to infect you.
4) Choosing a Robust Anti-Virus Protection
The volume of anti-virus protection software packages available far outweighs their true capacity. For this reason, it is often a daunting task to choose the right anti-virus protection. The following are some of the factors to consider while choosing the right kind of software for anti-virus protection:
- Reliability: It is important to check that the anti-virus software is not rendered useless by an existing software.
- Quality: The software under consideration should be robust enough to operate in aggressive and dynamic environments.
- Usability: Anti-virus software should be user-friendly so that it does not become a daily challenge for the users.
- End-to-end Protection: The program should be able to detect malicious code and also protect all channels or entry points to the computer — including email, the Internet, FTP, and more.
5) Keep your Anti-Virus updated
It is important to ensure that your anti-virus product is updated and operational, and rigorously scans your system for every new pop-up. These auto-scans are critical, as they can alert you on any external intrusion within your system.
Renewing the Anti-Virus product is critical on many fronts – it cleans up and secures the system from harmful virus, scans for probable attacks, detects malicious websites and files, blocks malicious software from getting automatically downloaded, and stalls any nasty pop-ups.
6) Build a Risk Management plan
Are you at ease with the idea that you have the best Risk Management and Data Recovery plan in place? You could be at risk. Even the best plans can go for a toss during major cyber-attacks, considering everything is connected and vulnerable. So, the idea is to be ready for the most unexpected problems in the ecosystem.
You can implement risk planning and identify potential problem that can lead to hiccups for the project or the application – analyze, identify, take action, and minimize the impact of the threat.
7) Build a Dependable Back-up System
The immediate response to this could be, ‘Yeah! We have stored all the information over the Cloud, and no one can encrypt it, as it is secure.’ Nevertheless, this might not work in a connected world where everything is interlinked and vulnerable to a cyber-attack or a malicious crypto-ransomware.
Scanning and Penetrating the data storage and back-up systems is indispensable today. For instance, Penetration Testing (referred to as pen testing) works to rigorously test the network, computer system, or Web application for any possible threats and weaknesses.
8) Dealing with Plug-ins and Ad-Blockers Effectively
It is essential to clean the system every once in a while, and remove outdated plugins and add-ons from all the browsers. Only the ones used daily deserve to remain, and care should be taken that they are updated to the latest version. Ad-blockers quell pop-ups from randomly surfacing and are quite effective when looking to avoid the threat of potentially malicious ads.
Enable click-to-play plugins. They keep Flash or Java from running unless you specifically tell them to (by clicking on the ad). The bulk of “malvertising” relies on exploiting these plugins, so enabling this feature in your browser settings will help keep the malware at bay.
9) Set up a Virtual Private Network
A Virtual Private Network (VPN) is a Virtual Private Network, is essentially used to anonymize traffic flowing through the Internet and secure it through encrypted connections and communication. A VPN creates a computer-generated point-to-point connection by employing dedicated connections, virtual tunnelling protocols and traffic encryption.
By using a VPN, you can significantly decrease your exposure to attackers on the look-out to identify and infiltrate any confidential data you send and receive over the internet.
10) Set up a Proxy
A proxy is a dedicated computer software which acts as a middleman between your computer and your Internet connectivity requests.
Heimdal Security, a proactive cyber security software, gives an insight to how a proxy works:
- You type CNN.com in your browser;
- The request goes to the proxy, which verifies it (you can upload blacklists of infected websites that the proxy can use to verify if the website is safe or not);
- If the website which you want to visit is safe, the proxy will show it to you;
- If the website you want to access is malicious, it’ll be blocked.
In Conclusion
Although there are many security measures, both for business as well as individuals, it becomes crucial to effectively conduct security testing for their applications.
Security testing is pivotal in a company’s business strategy. To overlook system and information security is akin to business suicide. As crucial as security testing is, and as useful as security testing tools are, the implementation process is highly customized to suit the need of the business. For this reason, it is important to have a trusted software security testing vendor.
Over the last decade, Cigniti Technologies has built capabilities, knowledge repository, and test accelerators leveraging experiencing working on over 100 engagements using best-of-breed testing tools, latest industry standards (OWASP, etc.) and proprietary testing methodologies.
Cigniti offers an in-depth security analysis supported by comprehensive reports and dashboards, along with remedial measures for any issues found. Cigniti has deep expertise in Security Testing for web applications, mobile application, software products, and web services, both on the premise and over the cloud.
To know more, visit our company website.




Leave a Reply